Last updated on August 6th, 2018
There always remains a concern for security flaws in an Android device. Well, Google has done its job. It cleared 90% of the malware apps from the Play Store. And also, security developers of CM Security have always helped the play store in detecting malware apps, combined effort by which the Google Play Store turned out to be cleaner than ever before.
Google Play Store is now safe and secure while there still exist some few apps which pose a threat remaining undetected. But you can decide your safety by downloading only the apps which are downloaded in numerous numbers and have a good rating. One should always read the reviews before installing an app even from Play Store. Talking about the Android OS, Lollipop is secure enough. Fortunately, this vulnerability has been patched on Android devices running on Android 4.4.4 or up. But you should consider testing your device against the vulnerability by the help of an app mentioned below.
The Anti-Virus won’t help you keep your device secure, if you are downloading apps from so-called “Untrusted Sources” or 3rd Party App stores. Everyone are well aware that they get the paid versions for free and also users download DATA+Apk game files along with cracked scores. Well, if you have no patience to score high in the game then you may not install it. But when you install the cracked version available, then there’s a chance that your device may get hijacked. So, the hackers want you to score more, while they too can score high by hijacking your device. Is that what you want for your Android device ?
What’s this Android Hijack Flaw ?

At Palo Alto Network : Security Research center, the senior system officials said that the vulnerability only affects the apps downloaded from 3rd party app stores. This vulnerability is termed as ” Time-of-Check to Time-of-Use ( TOCTOU ). A malicious app gets installed automatically using the vulnerability, and the app named “Android Installer Hijacking” hijacks your device. The hijacking happens when you install the Apk from an untrusted source. Here’s what happens : You feel good while downloading the app, and click on the security settings which allows installations from Untrusted sources. Then the app’s Package installer asks for your permission and finally you accept it. Do you think your Android device “will” be hijacked after you install it ? Well, your Android device gets already hijacked by the vulnerability when you accepted the permissions. You won’t find it anywhere, and it would seem to you, that there is no malicious behavior from the app. So, it is legitimate enough. But the vulnerability works without being seen and gets full access to your device.
What happen’s when my Android device gets Hijacked ?
Well, you are helpless after your Android device gets hijacked. If you are a PC analyzer at some point
concerned with security, you might be thinking that there’s no key logger or similar exploits in Android if you use an Anti-Virus app and a secure browser. But as I mentioned, your device has been hijacked. It get’s every single piece of your personal information (whatever it wants), like usernames, passwords etc.
How can I protect my device against that ?
Do you really think you can manually remove this type of installer when you can’t see it nor observe its behavior ? ? The first suggestion that comes to the scene, is to keep your Anti-Virus updated.
There might be a chance that they may have come up with a feature which prevents the installer to get into your device. Recommended Anti-Virus for Android devices are V3 Mobile 2.1, CM Security, Avast mobile, Bitdefender, Baidu, Quick Heal, 360-mobile, F-Secure and Trend Micro. So, there are lots of other options too, but these are the ones which give the best protection.
The one which gives the worst protection to Android devices include Anti-Malware by Malwarebytes and Trustlook. You should consider removing them as soon as possible. I don’t say this. Check out the AV-Test results to get a better knowledge of what I am trying to say.
Then the second best thing you could do is to stop downloading apps from untrusted sources ( including popular 3rd party stores )
How to Know whether my device is Affected ? ?
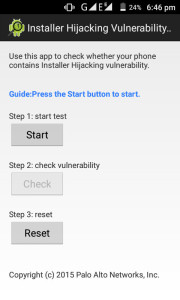
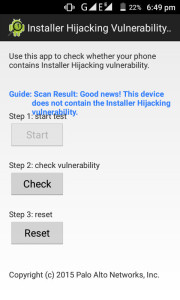
Thanks to Palo Alto Networks for developing an app “Android Hijack scanner” sized 1.1 MB. This app doesn’t actually scan that you are already affected or not. But it runs a simple test by which you can know whether your Android device is vulnerable to the hijack installer or not.
If it says that your device is vulnerable then you can figure out whether your device has been hijacked or not. Didn’t get? If you have installed any app from untrusted source then you can assume your device is affected. If you won’t assume then your credentials and information may be misused.
What to do if my device has been Hijacked ? ?
Well, if you know that you installed an app from a 3rd party app store then your device has been hijacked. To remove it you have one option of performing a Factory Data Reset. Before proceeding back up all your important files leaving behind the Apk files. And once again install all the necessary apps along with Anti-Virus only from Google Play Store. Till now there are no other methods to remove the hijack installer. Patches may be available from the vendors like Google, Amazon and others. And update your Android software if available via OTA or contact your manufacturer’s service center for manual upgradation process.
Featured Image credits : victoria white2010
WHAT IS THE CODING TO KNOW IF YOU HAVE BEEN HACKED, ON MAIN PC CODE HAD A SECTION OF DUMMY HOST, AND HAD MULTIPLE MOBILE LOG IN IS MY NETWORK HACKED WI-FI, NEED OPINION FAST THANKS
Please be clear about what you are asking. . I didn’t get what you want to know. . CODING to know ?? What does that mean ?? You have the Palo Alto app to detect the vulnerability. . So you don’t need any coding to check. If your device is vulnerable and you have downloaded apps from 3rd Party then just format your device backing up the internal storage.